If Google is serious about Android scams, there’s a bigger problem than sideloading is attracting attention across the tech world. Analysts, enthusiasts, and industry observers are watching closely to see how this story develops.
This update adds another signal to a fast-moving sector where product decisions, platform changes, and competition can quickly shape the market.
Affiliate links on Android Authority may earn us a commission. Learn more.
Google’s new sideloading rules have been announced, which add more friction to the process of installing apps from unverified developers. While the change is meant to stop certain types of scams, it ignores a bigger problem.
Google has set its sights on apps installed from other sources, but it doesn’t address the fact that millions of users are already exposed to malware through the official Play Store.
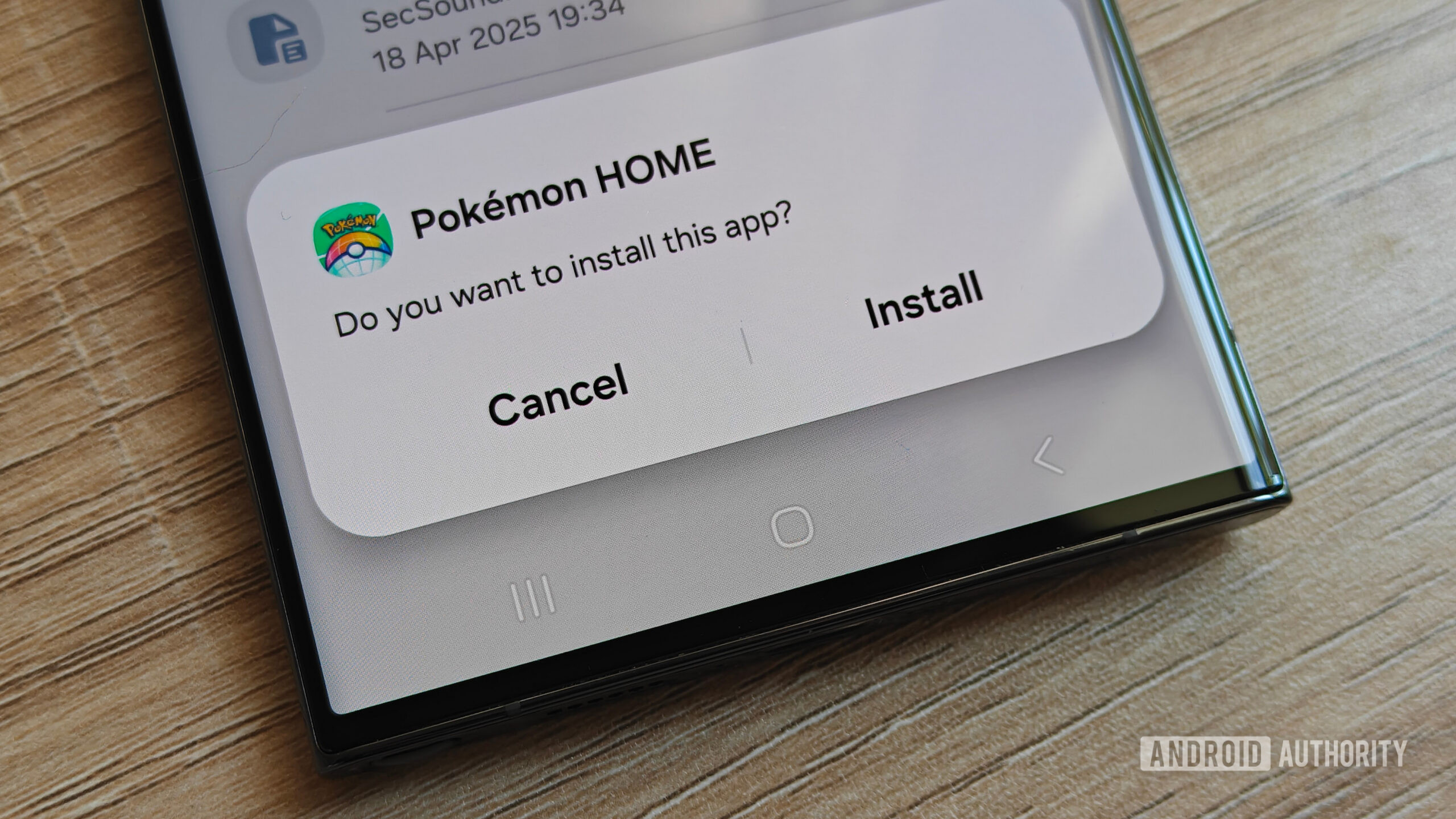
The new sideloading process, which will come into play in August, requires users to enable Developer Mode, confirm they’re not being coached, restart their phones, wait 24 hours for a security delay, and then enable the settings to allow them to install the app.
The good news is that this 24-hour process only needs to be completed once. But it’s a much longer flow than what users are accustomed to.
It also targets a very specific form of scam, where scammers pressure targets to install malware as part of a fake emergency. The sideloading process already has hurdles and warnings included, so Google’s new high-friction flow feels like overkill.
There already needs to be a lot at play for this type of scam to work. Some level of social engineering is usually needed, along with contact details for the target. The target then also needs to ignore multiple red flags during the process, as well as the existing warnings on their phone.
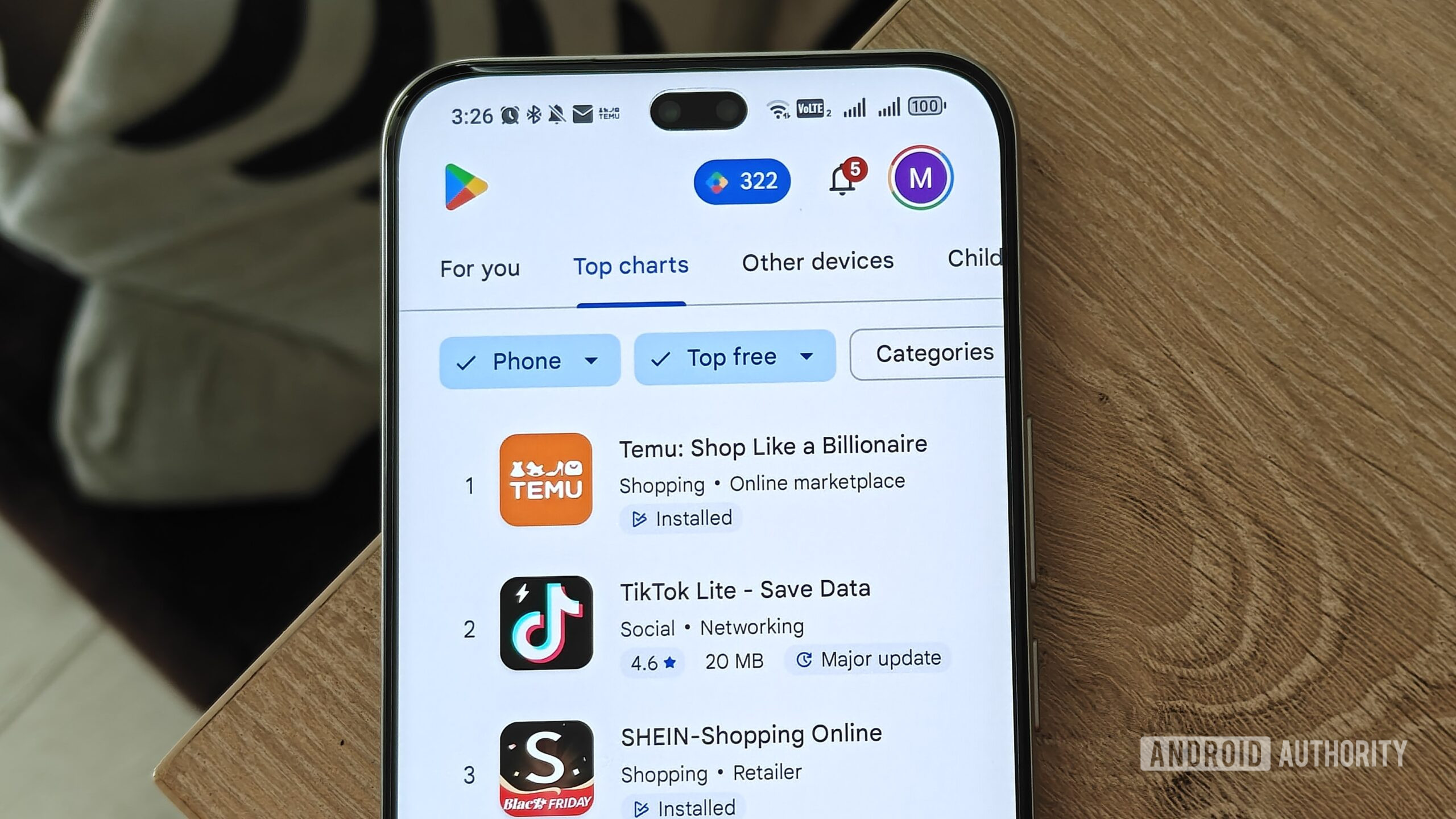
However, scamming people through the Play Store is seamless once the app makes it past Google’s filters — making it a way to reach millions.

While Google says that “all Android apps undergo rigorous security testing before appearing in Google Play,” plenty of malware still makes it onto the storefront. Sometimes, by the time these malicious apps are discovered, millions of people have already downloaded them.
for instance, researchers at Zscaler found 239 malicious Android applications on the Play Store that had attracted 42 million downloads between June 2024 and May 2025. This isn’t a once-off occurrence either.
Also in 2025, a Satori Threat Intelligence and Research Team found 224 malicious apps on the Play Store that had over 38 million downloads. These apps used devices to commit ad fraud. The apps specifically downloaded malicious code when users downloaded them after clicking on an ad that sent them to the Play Store listing.
Reports like these happen every year, with millions of users downloading malicious apps from the Play Store. The problem continues to grow, especially as apps are easier to churn out than ever using AI.
These apps often pose as utilities, games, or clones of apps from other brands, so it’s not as simple as just avoiding a specific type of app.
While Google does stop significant amounts of malware, many malicious apps still end up on the storefront — where they come with no warnings when a user installs them. Even the data safety section, which is meant to give users more information about permissions and how their information is used, relies on what the developer discloses.
Another problem with Play Store malware is how easily these apps can be surfaced through online ads. Some ads automatically open the Play Store when they end, or make the dismiss button so tiny that users end up on the Play Store when trying to close an ad.
Since the Play Store is presented as a trusted source for apps, users are less likely to raise an eyebrow when compared to a random website or APK.
Once an app is on your device, you don’t get warnings about granting sensitive permissions such as the ability to display over other apps.
Until the Play Store’s malware problems are addressed, it remains the primary way scammers can target people. This sentiment has been echoed by some of our readers and YouTube viewers, some of whom only encounter malware on the Play Store.
From my own experience, the current sideloading process already gives users ample warning. Yet the Play Store attracts implicit trust despite its flaws.
The first and only time I sent my mother an APK to download, she asked me if it was safe once her phone warned her it could be malicious. It was for the HUAWEI Health app, which she needed for her smartwatch. Because of the HUAWEI ban, the app is no longer available on the Google Play Store, regardless of where you live.
On the other hand, I’ve had to advise people I know against using certain apps they got from the Play Store due to dodgy permissions and features. This included a family member with an app that was mining crypto using their phone.
I would see Google’s new sideloading process with more optimism if I felt like the company was really committed to improving the safety of its users. But this so-called fix makes life difficult for open-source developers who don’t want to register with Google, while still leaving many Play Store problems unaddressed.
I feel like all the company has managed to do is make sideloading more frustrating. Meanwhile, regular Play Store users are left with a false sense of security.
Thank you for being part of our community. Read our Comment Policy before posting.
Why This Matters
This development may influence user expectations, future product strategy, and the competitive balance inside the broader technology industry.
Companies in adjacent segments often react quickly to similar moves, which is why stories like this tend to matter beyond a single announcement.
Looking Ahead
The full impact will become clearer over time, but the story already highlights how quickly the modern tech landscape can evolve.
Observers will continue tracking the next steps and how they affect products, users, and the wider market.



